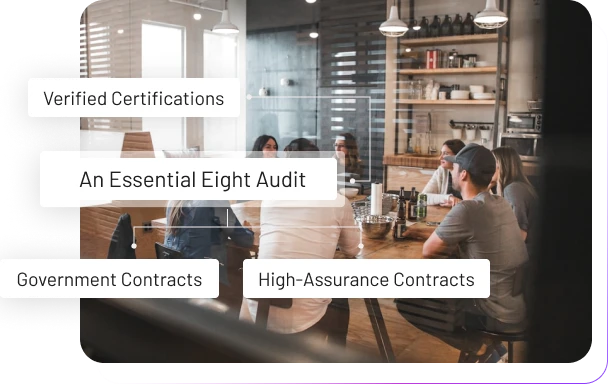
Get Your External Independent E8 Audit Requirements
An Essential Eight Audit is required to formally verify your defense posture for many government and high-assurance contracts. We provide the independent, expert verification required to certify your environment's adherence to the ACSC's Maturity Model (ML0-ML3).
Request for Free Compliance Check
Why an Independent E8 Audit is Critical
As a mandatory element of GRC for organisations dealing with Australian Government data, an E8 Audit provides the formal evidence needed to satisfy contractual and regulatory obligations.
Contractual Obligation
Satisfy Compliance: Provide the definitive, third-party report required to prove your E8 Maturity Level (e.g., ML3) to contract holders.
Risk Assurance
Objective Verification: An external auditor provides an unbiased assessment, validating or challenging internal claims about your security posture.
Executive Governance
Accountability: Formal evidence that management is meeting its duty of care by implementing and maintaining the required security controls.
Pre-Accreditation
Readiness Check: Identify any fatal flaws in your E8 implementation before a full, high-stakes ISM, IRAP or RFFR accreditation audit.
Our Essential Eight Audit Process
We strictly follow the audit guidance provided by the Australian Cyber Security Centre (ACSC) to ensure a high-assurance, defensible assessment of your environment.
Audit Deliverables & Assurance
Official ACSC Provided E8 Audit Report
A formal, signed document stating your confirmed E8 Maturity Level and the technical evidence for the score.
A matrix showing the compliance status ("Effective," "Ineffective," or "Alternate Control") for every requirement within each of the eight strategies.
Formal review of any security exceptions, ensuring they are documented, approved, and backed by appropriate compensating controls.
Achieve defensible E8 compliance with an objective, expert-led audit.
Schedule Your Essential Eight Compliance Audit