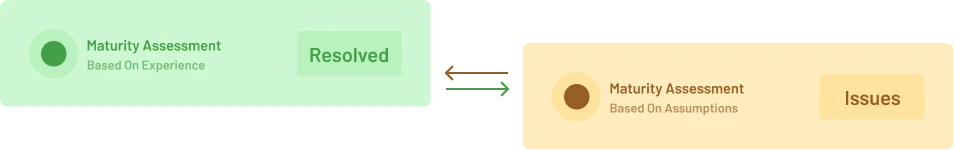
Know Your Real Security Posture. Achieve Compliance Certainty.
Your security strategy must start with facts, not assumptions. We deliver a comprehensive Cybersecurity Maturity Assessment based on your risk profile, measured against global frameworks (ISM, PSPF, Essential Eight).
Request for Cybersecurity Maturity Assessment
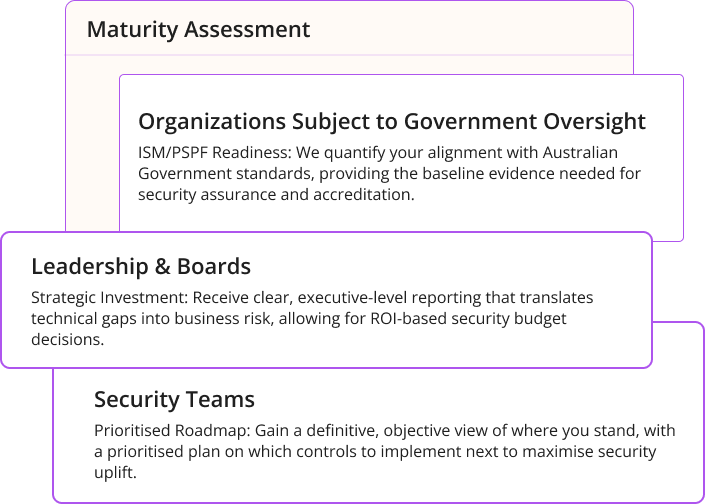
Why Conduct a Maturity Assessment?
A maturity assessment goes beyond a simple audit; it provides an actionable blueprint for strategic security investment, ensuring every dollar spent reduces your highest risks.
Our Risk-Based Assessment Process
We deliver a comprehensive solution—from initial assessment to a fully prioritised action plan—ensuring your security environment is built on intelligence, not assumptions.
Key Frameworks Assessed
We provide expert assessment against the frameworks essential for operating securely and compliantly in high-assurance environments:
ISM (Information Security Manual)
Deep-dive assessment of controls across governance, personnel, and system security for handling Australian Government data.
PSPF (Protective Security Policy Framework)
Evaluation of your security governance, personnel security, and information security policies.
Essential Eight
Measurement of your preventative defense capabilities across the 8 key strategies (e.g., Application Control, MFA) to determine your Maturity Level (ML).
Stop guessing your risk. Get a validated, actionable security plan.
BOOK YOUR FREE CONSULTATION