Phase 1: Assessment & Strategy
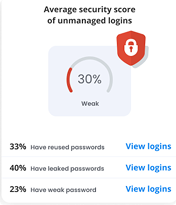
Risk-Based Content Audit: Analyze your organisation’s threat profile from Cyber Threat & Risk Assessment (CTRA) and identify the specific human behaviors contributing to the most significant risks (e.g., weak passwords, social engineering).
Gap Analysis: Map your current training content against required compliance frameworks (e.g., mandatory topics under ISM, annual refresher requirements).
Target Audience Definition: Identify key user groups and design a strategy based on their technical aptitude, job roles, and specific access privileges.